Attack Chain Intelligence
We don't just find vulnerabilities. We map how they chain together into real attack paths that adversaries actually use.
Scored Attack Chains
Knowledge Graph Edges
MITRE Techniques
Chain Stories
Chain Severity Distribution
Evidence Bands
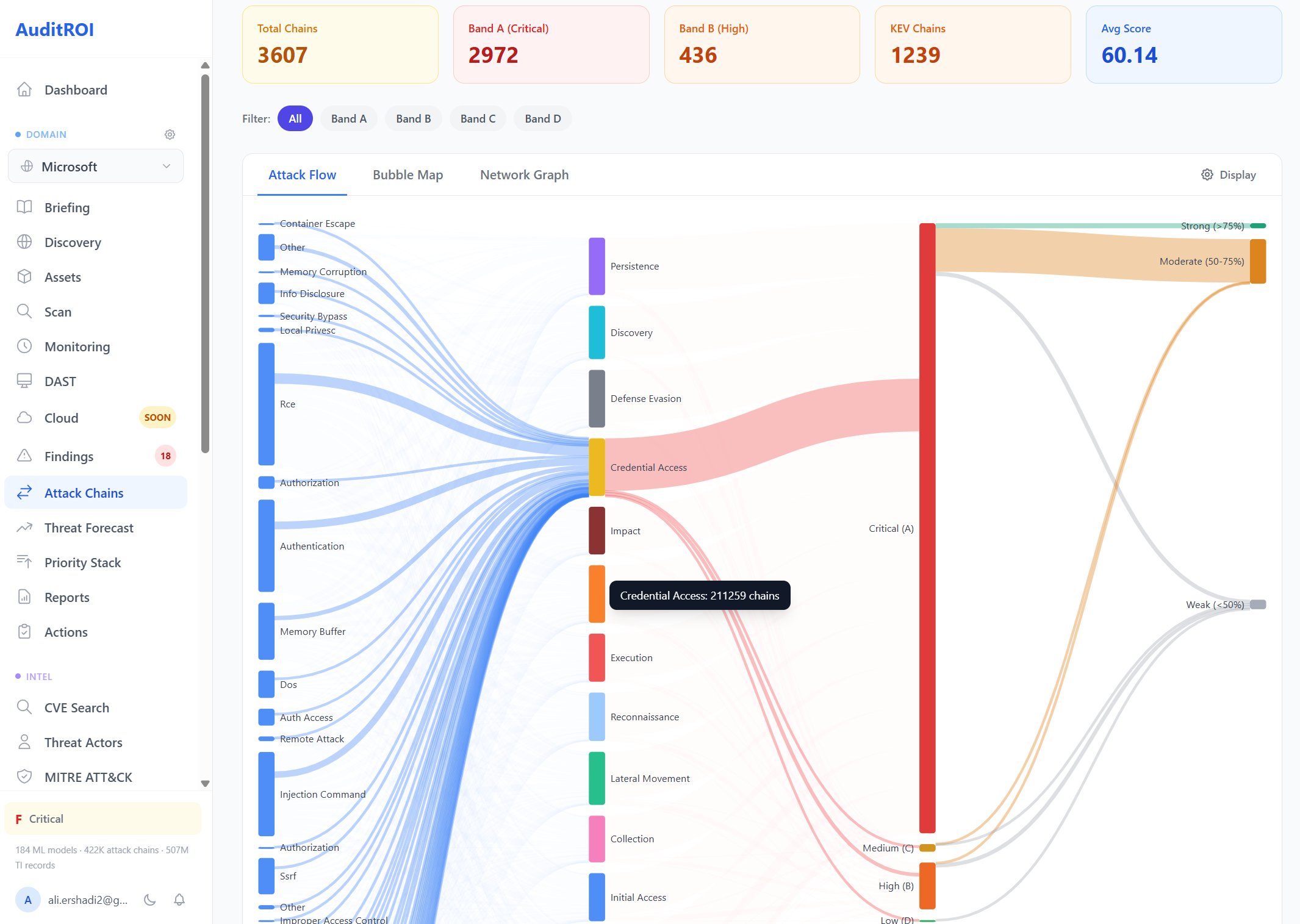
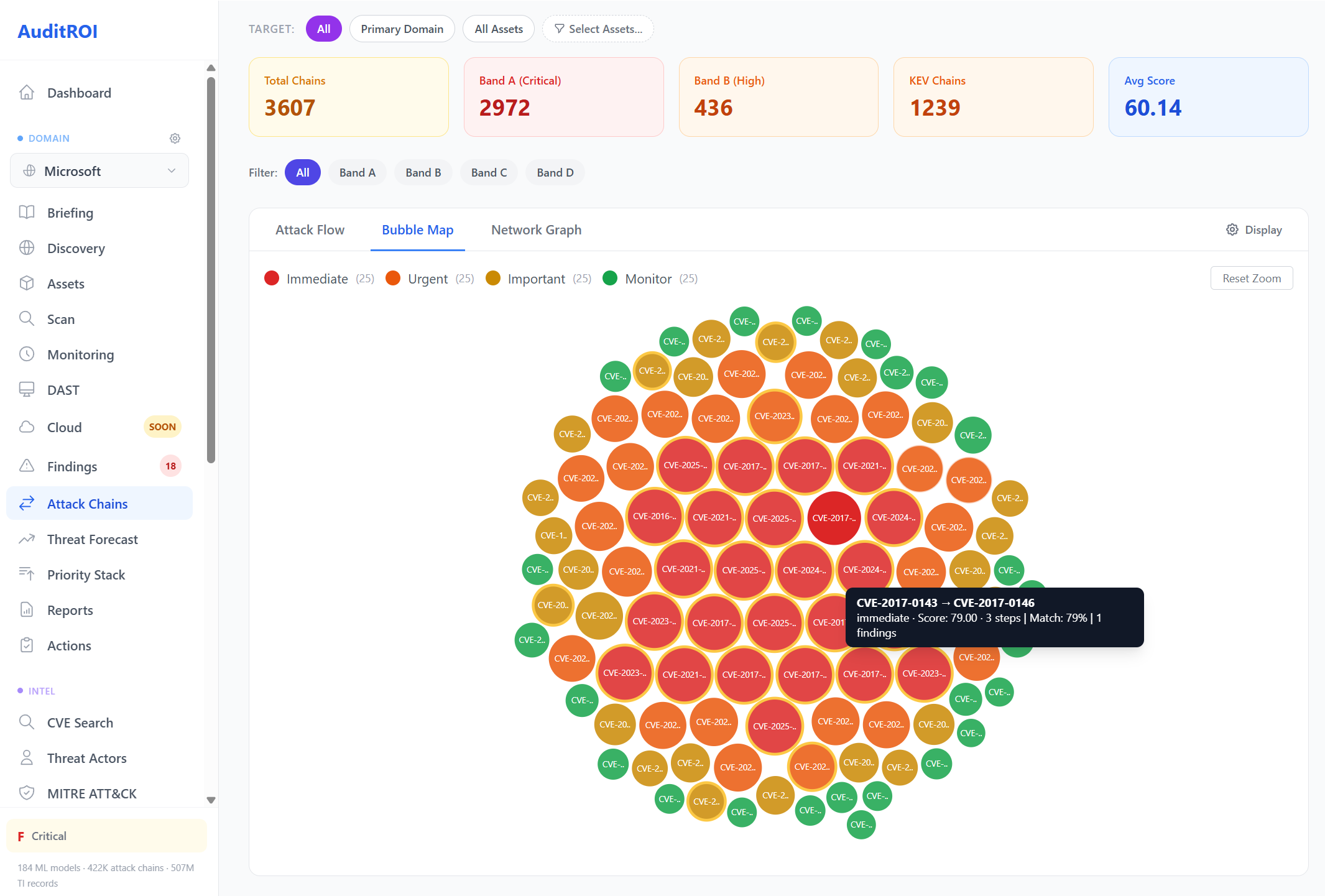
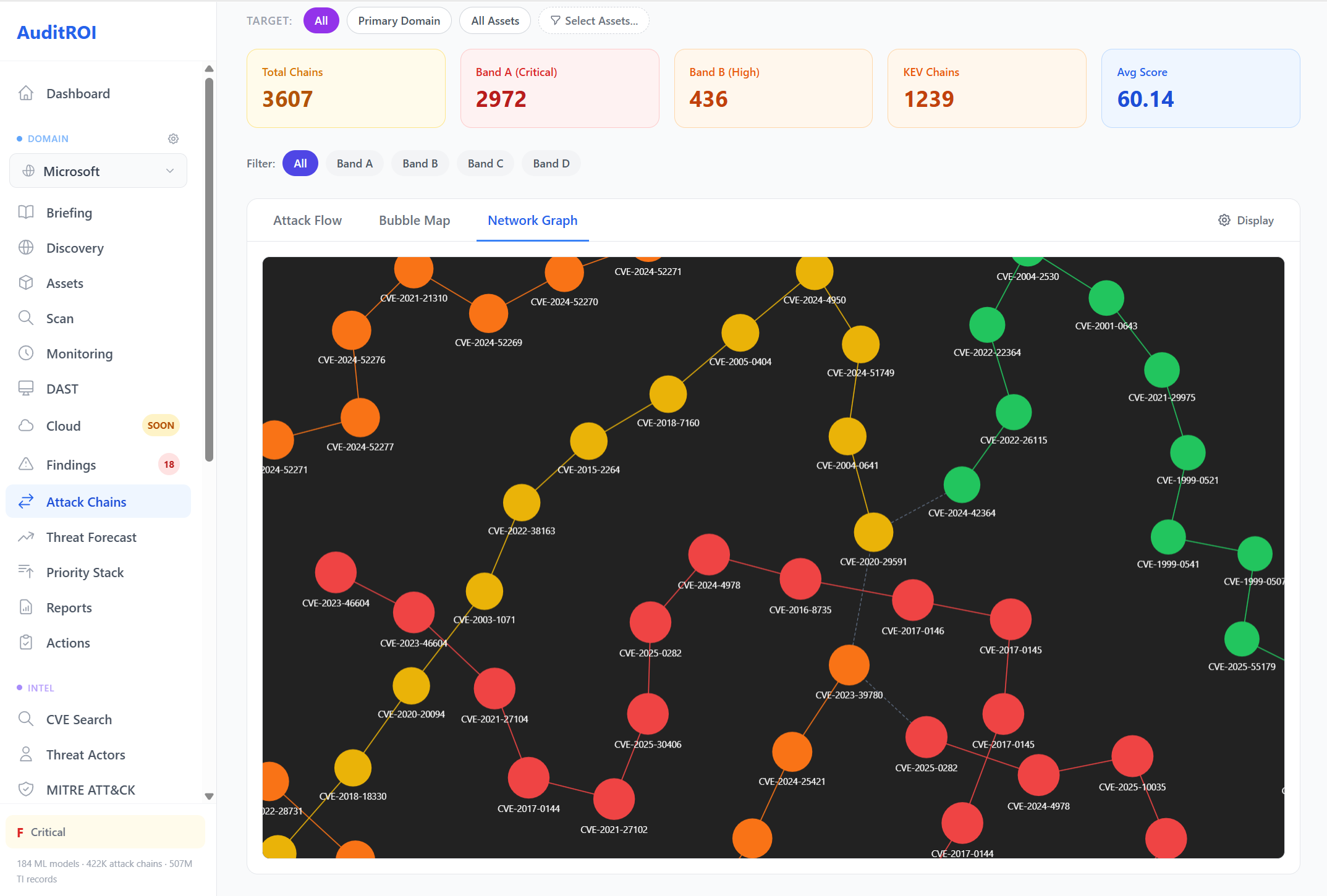
Attack Chain Visualizations
Three interactive views to explore how your vulnerabilities chain together into real attack paths. Each visualization reveals different patterns — flow relationships, cluster density, and interconnection topology.
Click any image to enlarge and browse the full gallery.

Attack Flow (Sankey)
Vulnerabilities chaining through MITRE techniques to impact.
Bubble Map
Severity-coded clusters showing CVE relationships at a glance.
Network Graph
CVE interconnections through shared techniques and attack paths.
Chain Intelligence Detail
Browse 422K+ scored attack chains filtered by severity band. Drill into any chain for kill chain phase coverage, linked MITRE techniques, and matching Sigma detection rules. Each chain gets a composite score based on exploitability, confidence, and impact.

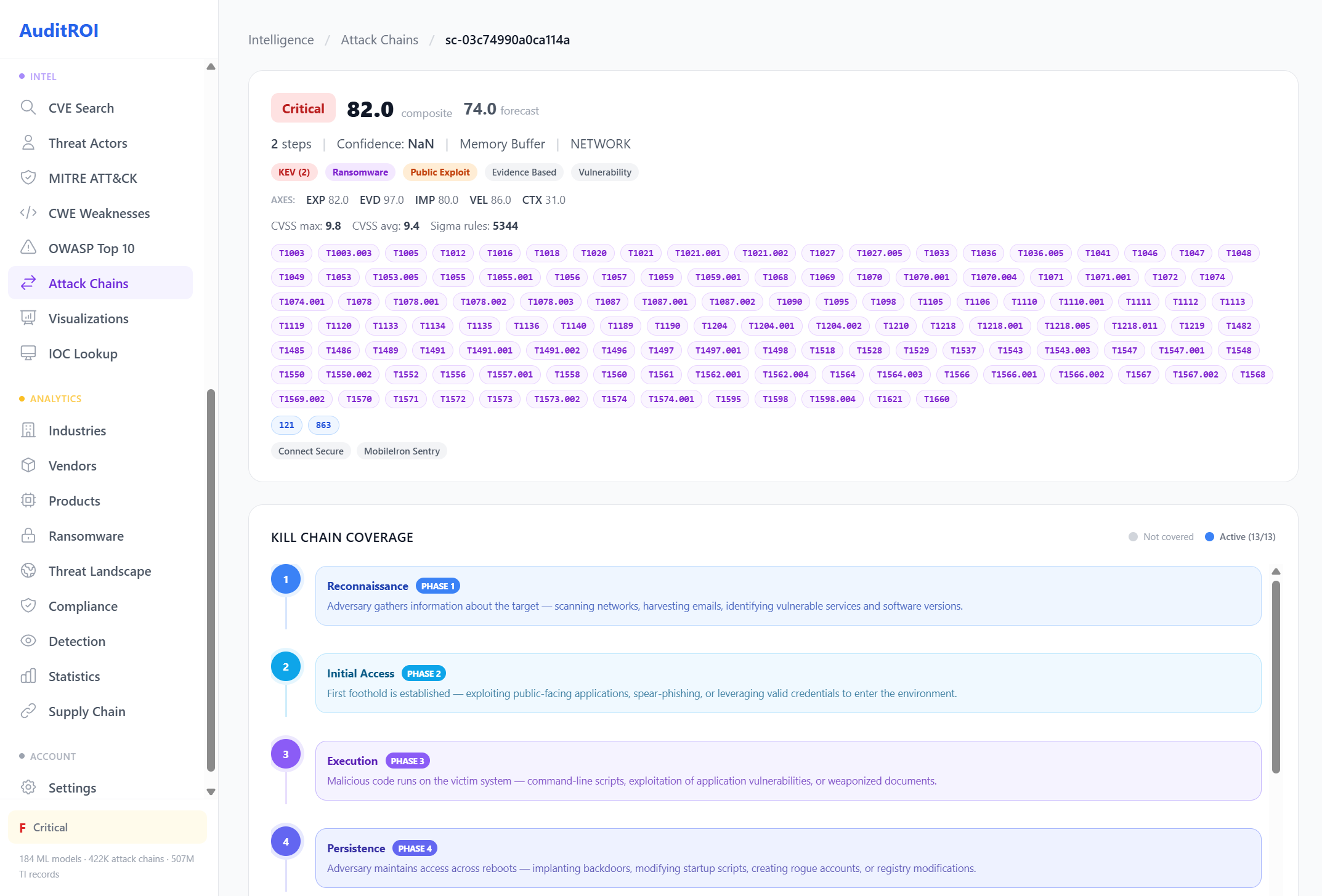
Kill Chain Coverage
Attack chains mapped to every phase of the MITRE kill chain with detection coverage.
Map Your Attack Surface
See how your vulnerabilities chain together. Free scan, instant results.