See What's
Inside
From security briefings to ransomware economics, from CVE intelligence to compliance mapping. Explore every feature that makes AuditROI the most comprehensive security intelligence platform.
Command Center
Threat Intelligence
Analytics
Compliance & Discovery
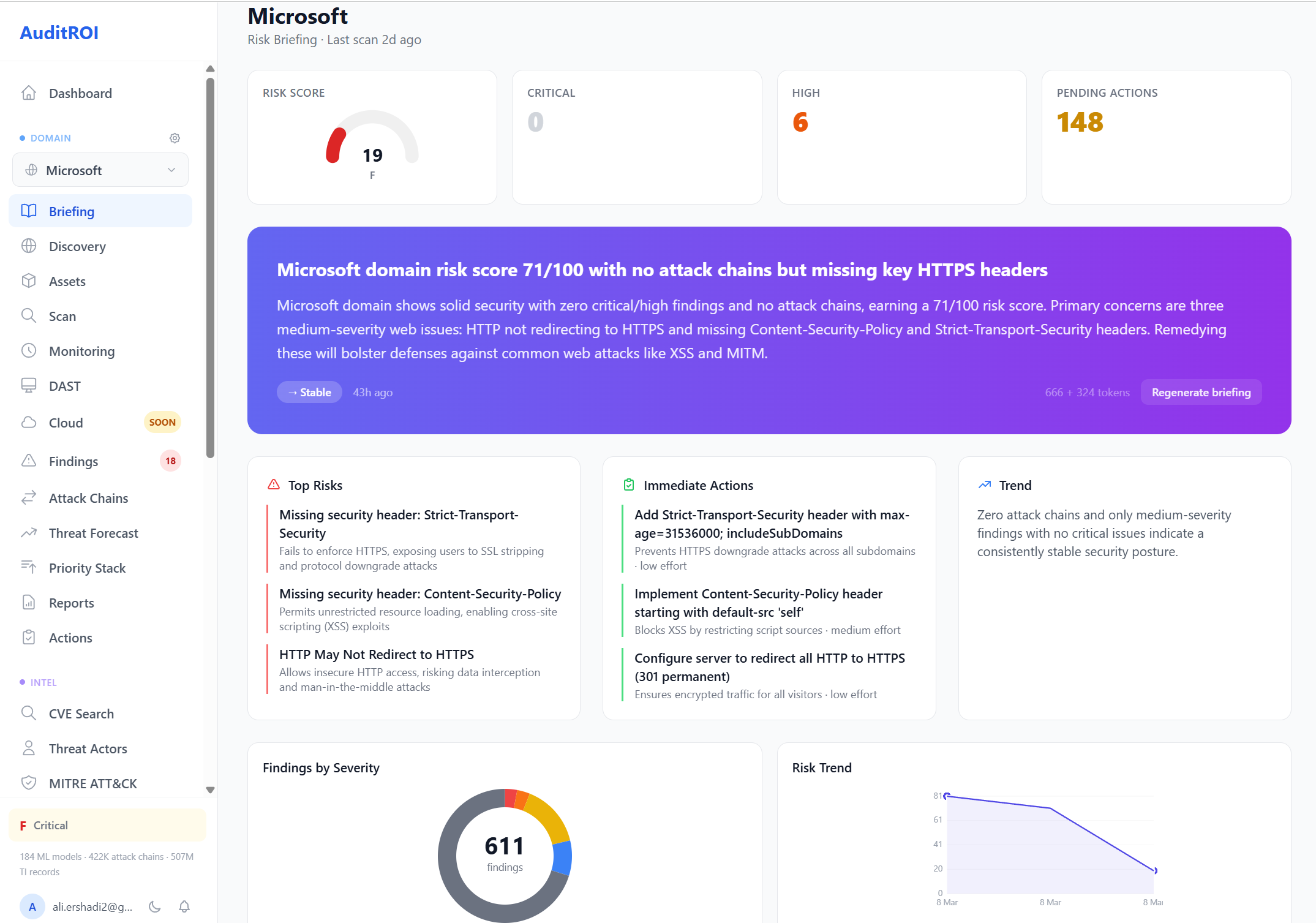
Security Briefing
Your daily security status at a glance. AI-generated risk assessment, severity breakdown, and prioritized actions.
Every morning, AuditROI distills your scan results into a single-page briefing: an overall risk grade, a plain-language AI summary of what changed overnight, a severity breakdown by category, and a ranked list of recommended next steps. Click the image to explore the full interface.
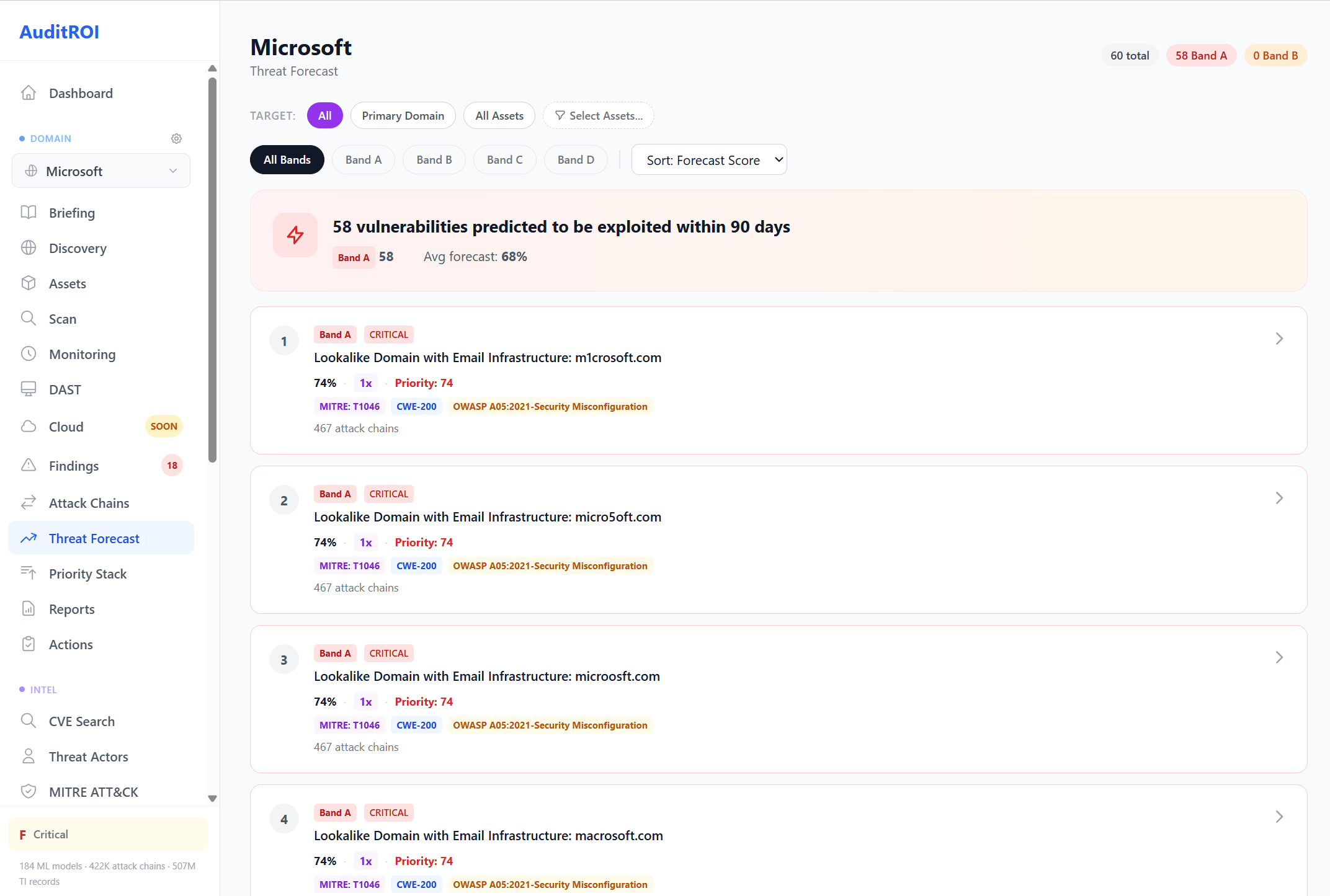
Threat Forecast
ML-powered exploit prediction. Know which CVEs will be weaponized before they trend on Twitter.
The forecast model analyses exploit maturity signals, social-media chatter, dark-web mentions, and EPSS scores to predict which vulnerabilities are most likely to be weaponized in the next 30, 60, and 90 days. Each CVE is scored with a confidence band so you can prioritize patching before the exploit lands.
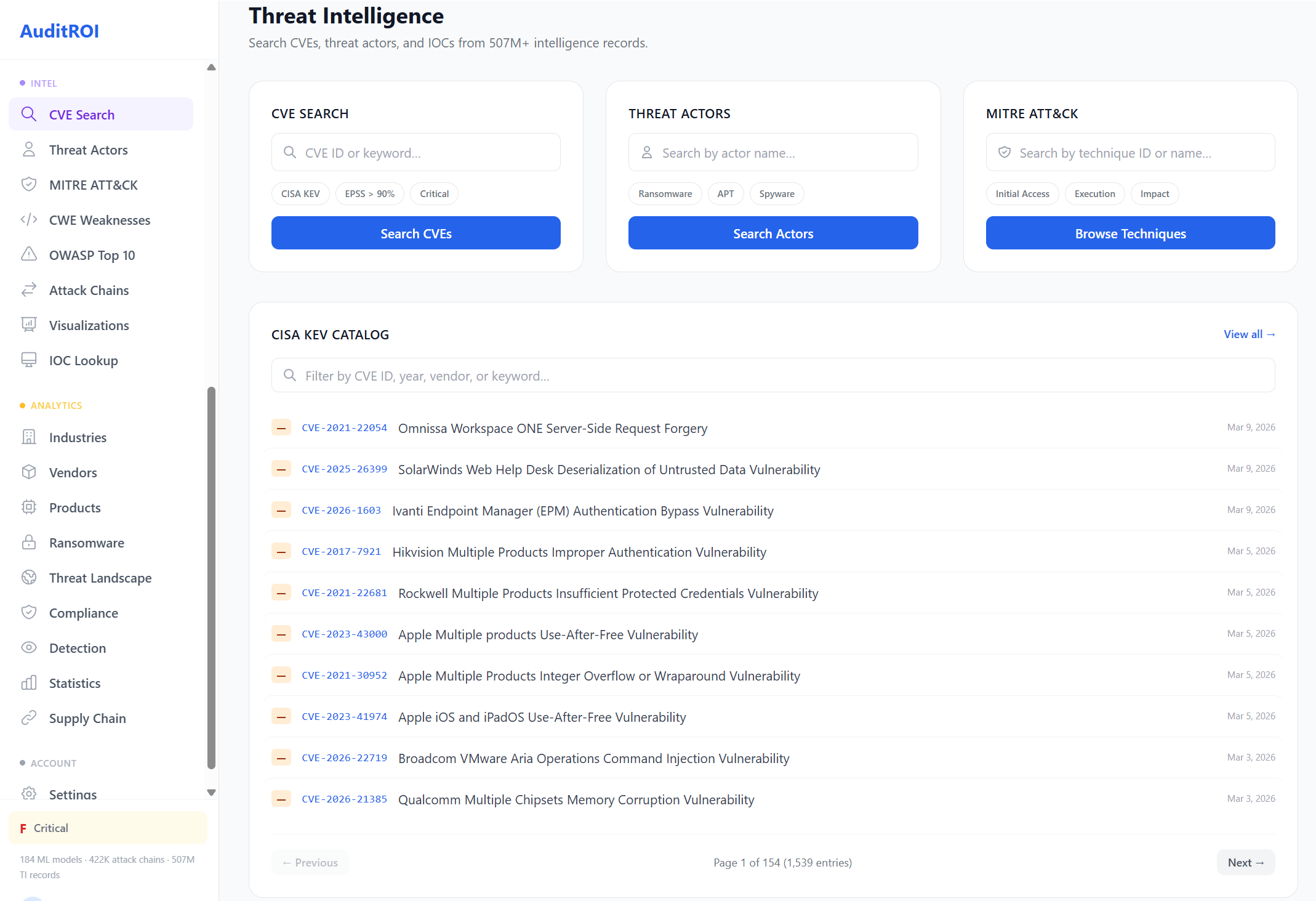
Intelligence Console
200K+ CVEs, 900+ threat actors, MITRE ATT&CK mappings, and live CISA KEV tracking. All in one searchable console.
Search any CVE to see its CVSS and EPSS scores, known exploits, linked ransomware groups, and patch availability. Cross-reference threat actors with their MITRE techniques, or browse the full CISA Known Exploited Vulnerabilities catalog filtered to your stack.
Search 200K+ CVEs with EPSS, exploit status, and patch info
900+ actors with MITRE techniques and IOC tracking
1,042 techniques with detection rule coverage
Ransomware Intelligence
Economics, group profiles, IOC tracking, and victim analysis. Understand the ransomware threat landscape with data, not fear.
LockBit
RussiaALPHV/BlackCat
RussiaCl0p
RussiaPlay
UnknownAkira
UnknownRoyal
RussiaThreat Actor Database
900+ threat actors profiled with MITRE techniques, IOC feeds, campaign history, and attribution data.
APT29 (Cozy Bear)
Russian SVR-linked group targeting government and diplomatic organizations worldwide
Lazarus Group
North Korean state-sponsored group focused on financial theft and cyber espionage
LockBit
Prolific RaaS operation with 1,400+ victims across all industries globally
Volt Typhoon
Chinese state-sponsored group targeting US critical infrastructure systems
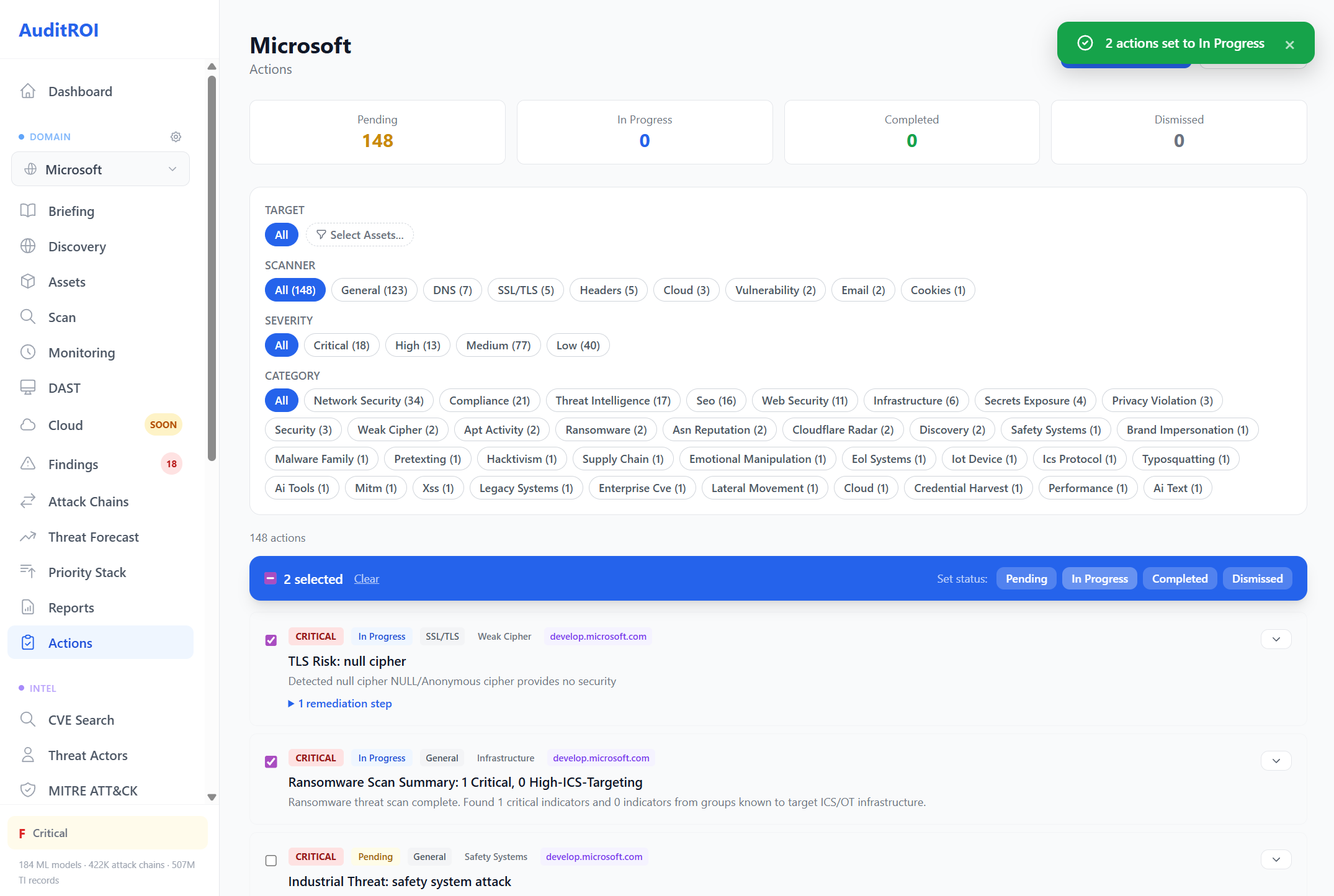
Action Center
Prioritized remediation playbooks with step-by-step guidance, effort estimates, and provider-specific instructions.
Every finding from your scans is translated into a concrete remediation task. Filter by scanner category or severity, batch-assign actions to your team, and follow provider-specific fix instructions with estimated effort and impact. Turn audit findings into a trackable remediation workflow.
Detection Engineering
21,000+ detection rules mapped to 1,042 MITRE ATT&CK techniques. Sigma, YARA, and Nuclei coverage analysis.
Global Threat Landscape
| Country | Code | Malicious IPs | C2 Servers |
|---|---|---|---|
| China | CN | 423K | 8.2K |
| United States | US | 312K | 6.1K |
| Russia | RU | 287K | 4.9K |
| India | IN | 156K | 2.1K |
| Brazil | BR | 98K | 1.8K |
Every Feature, One Platform
12 more capabilities spanning compliance, discovery, supply chain, industry intelligence, and beyond.
CVE Intelligence Hub
200K+200K+ CVEs with EPSS trends, exploitation status, and CISA KEV catalog
Threat Actor Database
900+900+ actors with MITRE techniques, IOC tracking, and campaign history
TI Alerts
6 typesReal-time alerts for exploit publications, ransomware watch, and KEV additions
Threat Landscape
214 countriesWorld choropleth map, country risk tables, and temporal threat trends
Industry Intelligence
17 industries17 industries profiled with breach costs, compliance mapping, exploit rates
Verified Statistics
17,89017,890 verified breach statistics with citations from authoritative sources
Supply Chain Risk
226 profiles226 industry-vendor risk profiles for third-party assessment
Compliance Mapping
18 frameworksGDPR, HIPAA, PCI-DSS, SOC 2 automated assessment with 171K CVE mappings
Detection Engineering
21K+ rulesSigma, YARA, Nuclei rule coverage across 1,042 MITRE techniques
Discovery (EASM)
10K+ assetsSubdomain enumeration, IP discovery, service detection, DNS record analysis
Findings Dashboard
ML scoringSeverity distribution, status tracking, composite scoring, kill chain indicators
Scan Orchestration
266 scanners266 scanners, 21 scan bundles, real-time progress, scheduled monitoring
Ready to See It Live?
Start with a free security audit. No credit card, no agents to install, results in minutes.