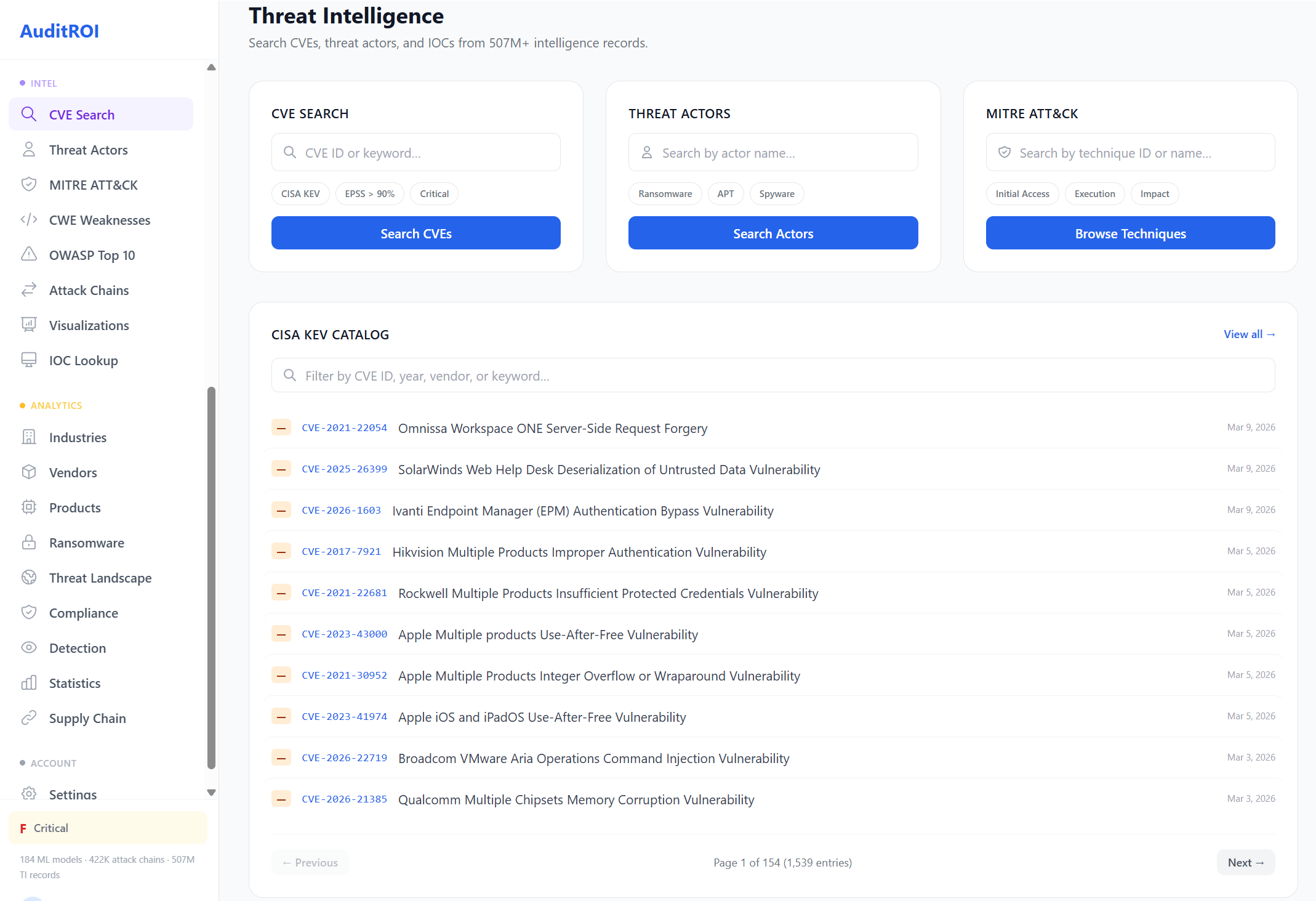
Threat Intelligence Database
507M+ records from 49+ sources. Every vulnerability enriched with exploit data, ransomware attribution, and predictive scoring.
Million Records
Data Sources
Tables
Exploit Forecast AUC
Exploit Forecast AUC
Our ML model predicts whether a CVE will be exploited in the wild within 90 days, using 328 features across vulnerability characteristics, threat actor patterns, and exploit ecosystem signals.
Intelligence Categories
Ransomware Economics
Real-time economics tracking across 318 ransomware groups with year-over-year trends.
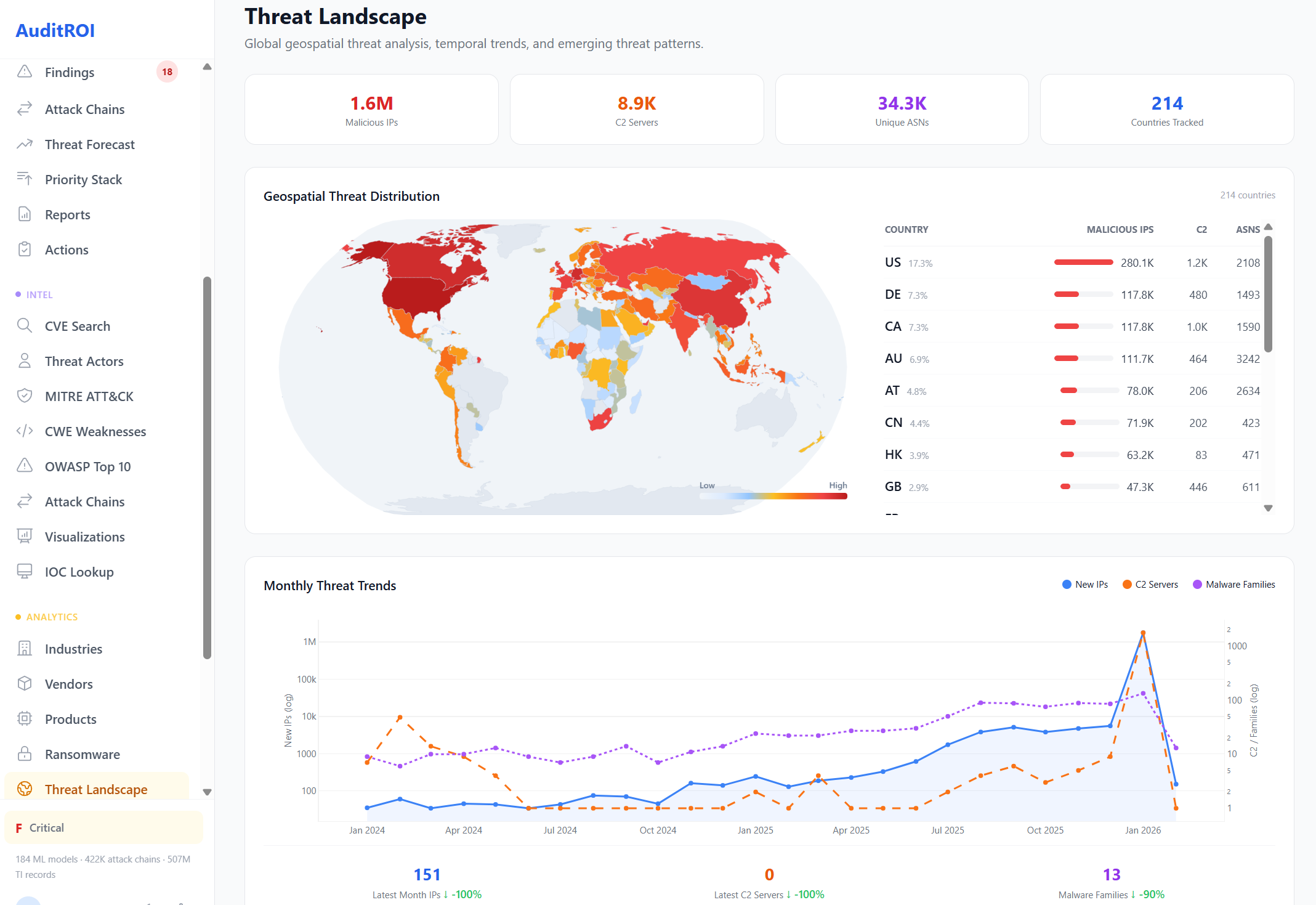
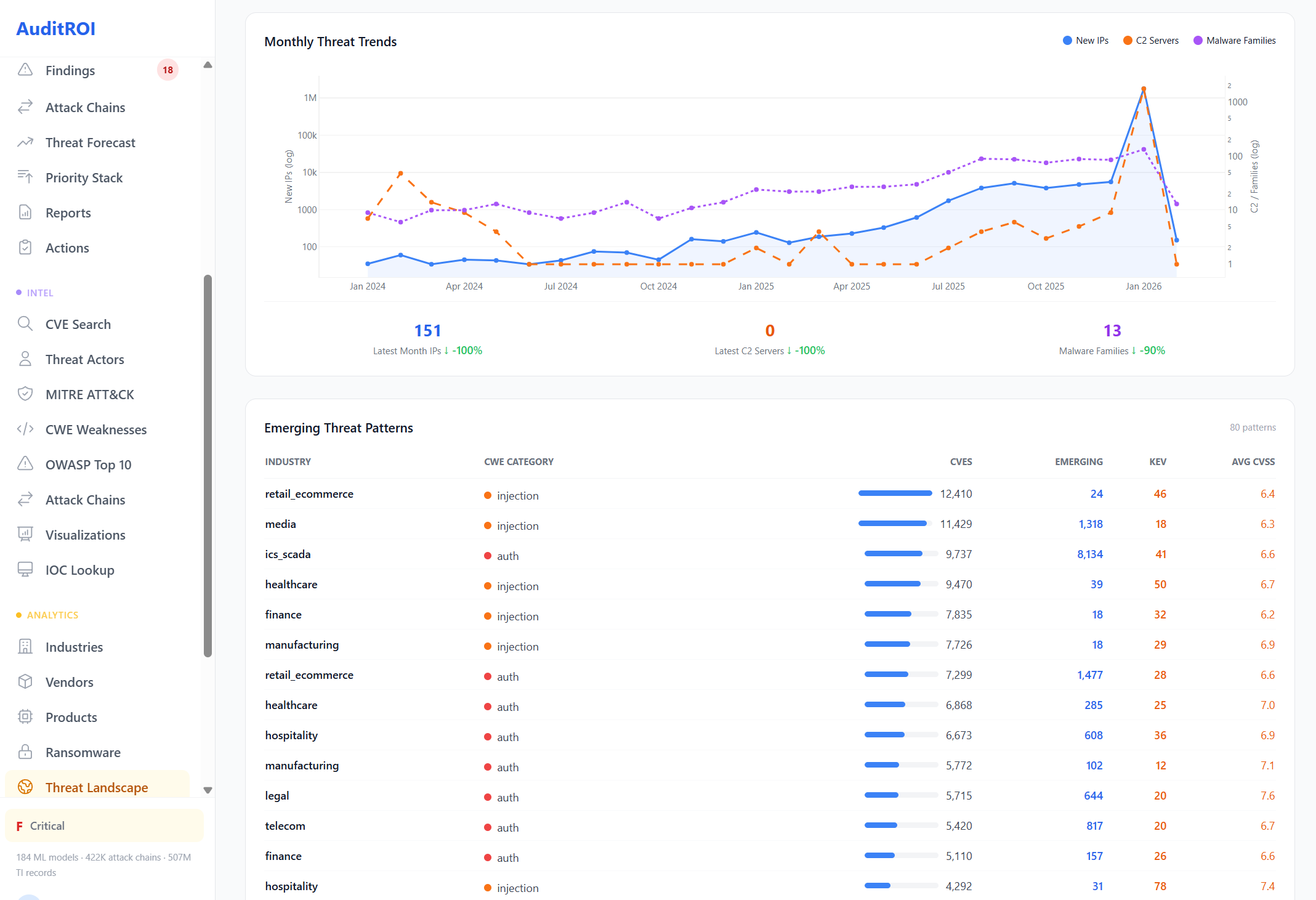
Global Threat Landscape
214 countries profiled with malicious infrastructure, C2 server counts, and geo-threat intelligence.
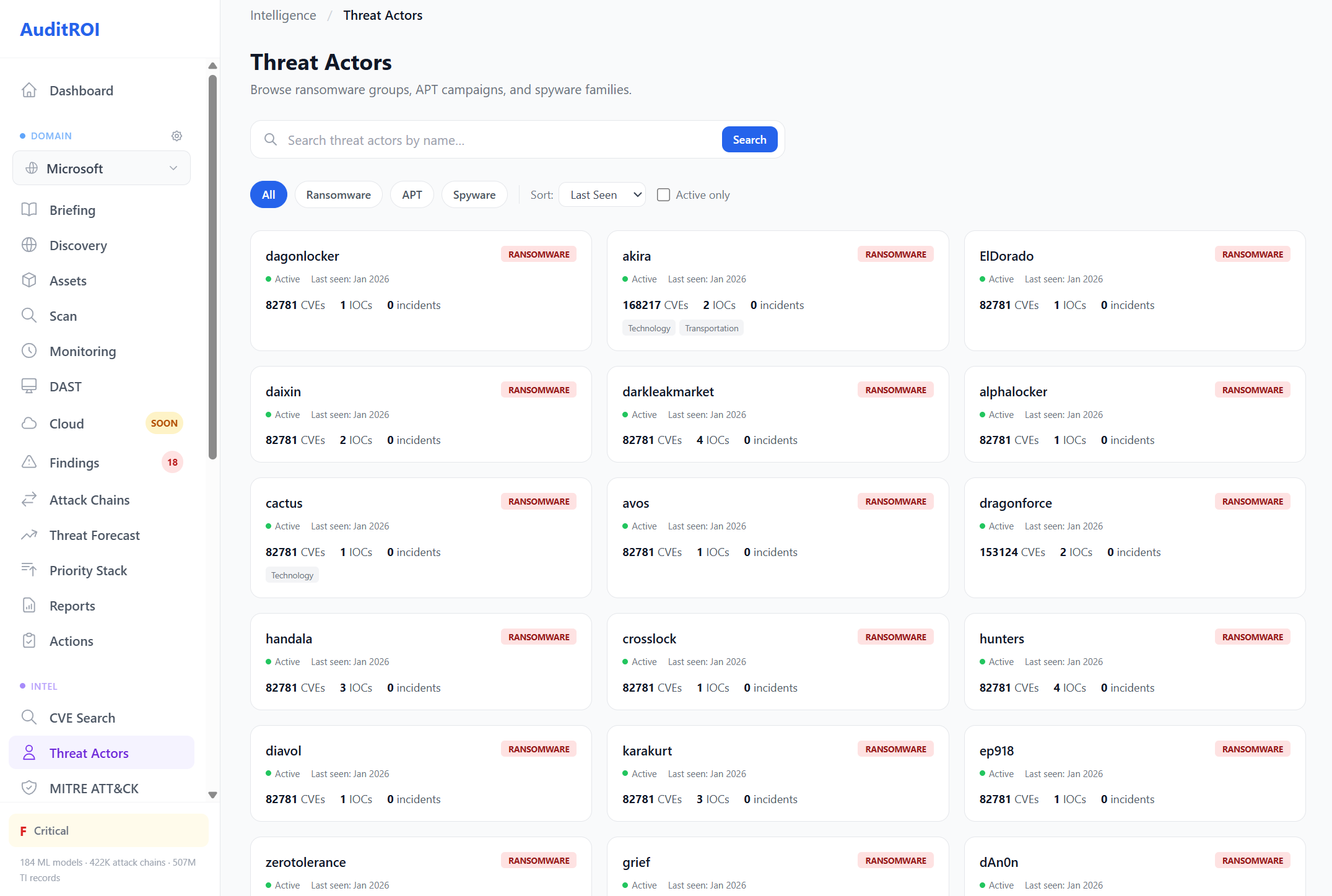
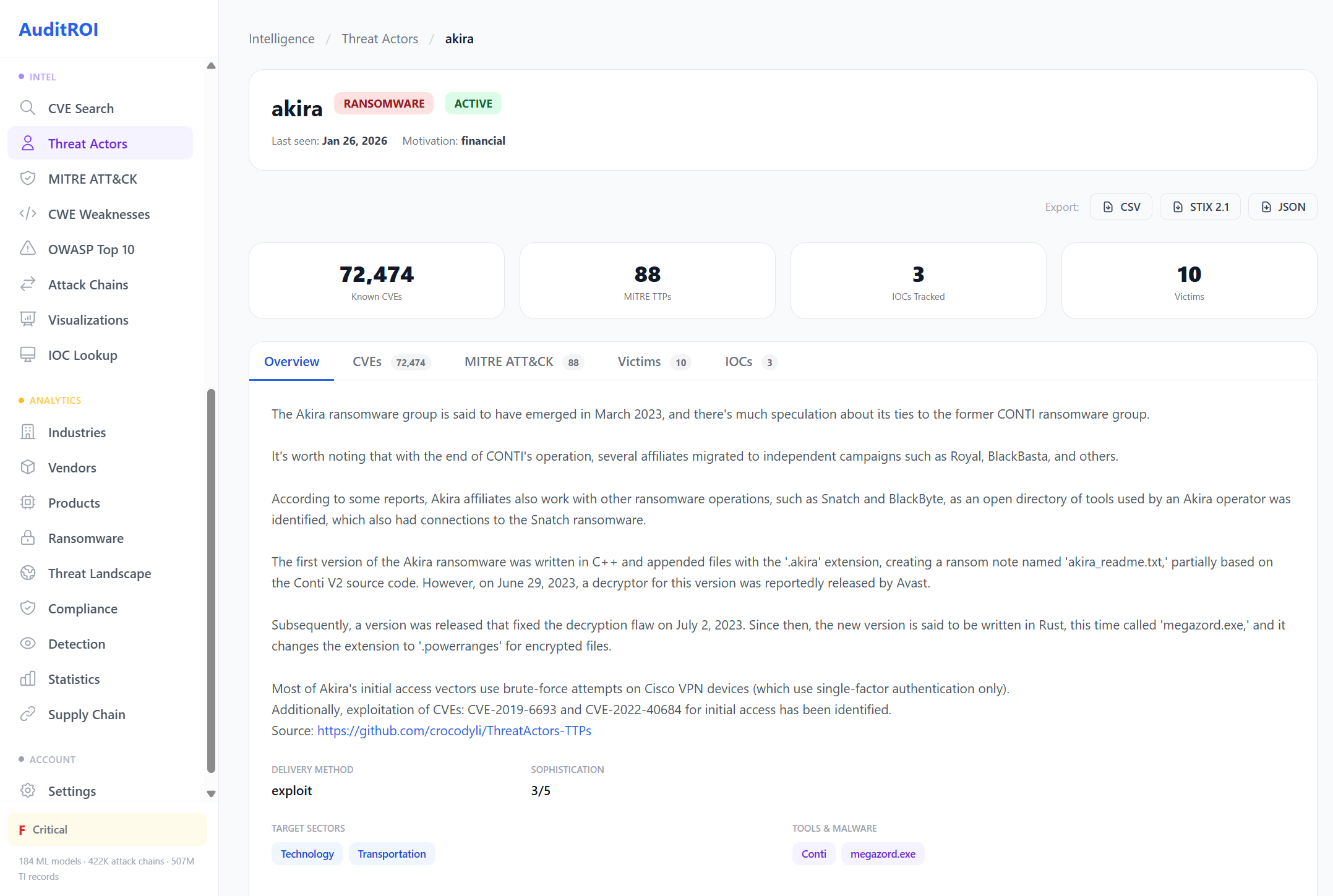
Threat Actor Profiles
900+ actors with MITRE ATT&CK technique mappings, IOC feeds, and campaign attribution.
APT29 (Cozy Bear)
Russia · 47 techniques · 3,200 IOCsRussian SVR-linked group targeting government and diplomatic organizations worldwide
Lazarus Group
North Korea · 38 techniques · 2,800 IOCsNorth Korean state-sponsored group focused on financial theft and cyber espionage
LockBit
Russia · 28 techniques · 2,847 IOCsProlific RaaS operation with 1,400+ victims across all industries globally
Volt Typhoon
China · 22 techniques · 1,500 IOCsChinese state-sponsored group targeting US critical infrastructure systems
Intelligence Modules
Deep-dive reference databases covering every major security framework. Each module is fully searchable, cross-referenced with CVEs, and linked to detection rules.
Click any screenshot to enlarge and browse the full gallery.
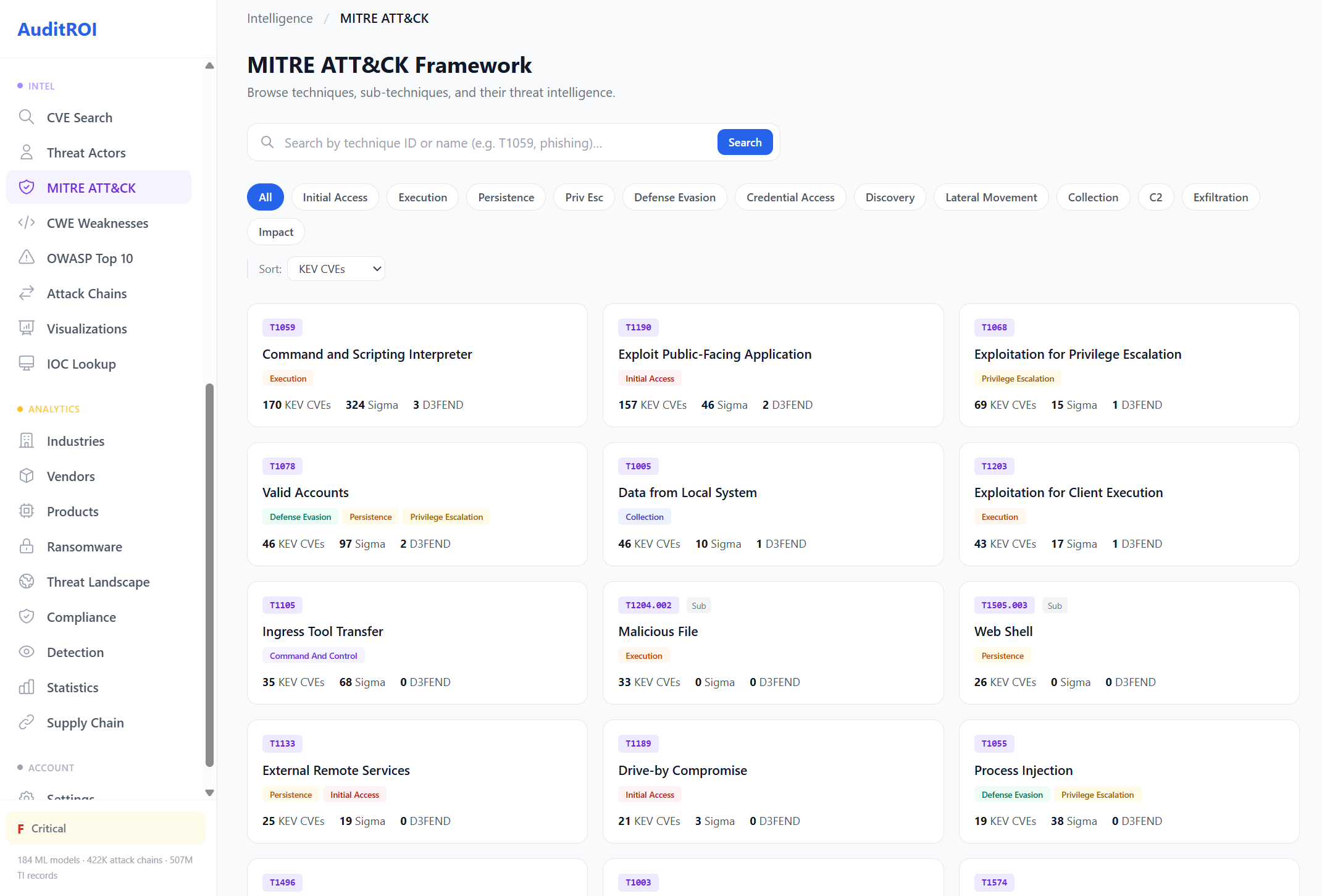
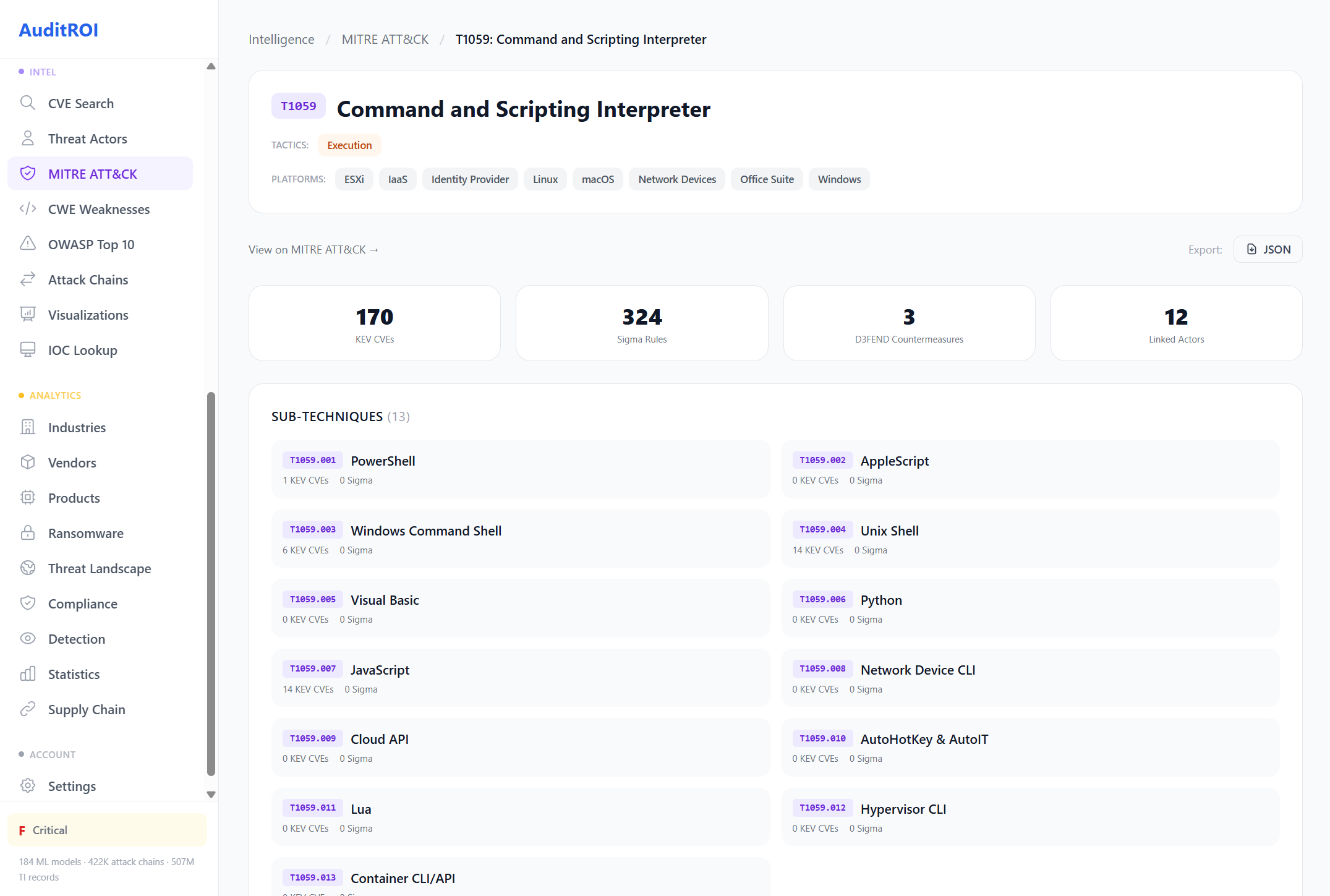
MITRE ATT&CK Framework
Browse all techniques and sub-techniques with linked CVEs, Sigma detection rules, and threat intelligence context.
Filter by tactic phase, search by technique ID or name. Each technique shows KEV CVE count, Sigma rules, and related threat actors.
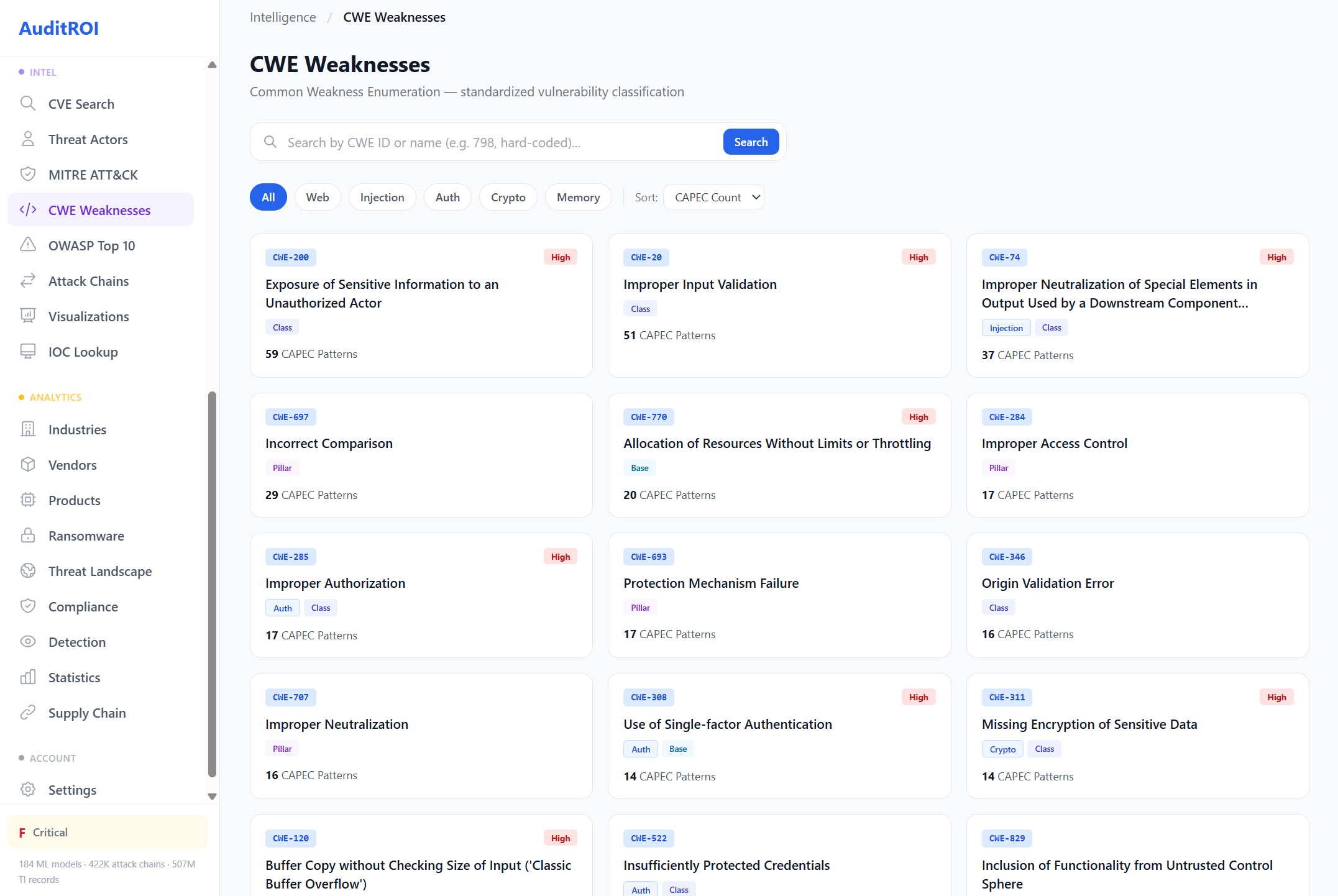
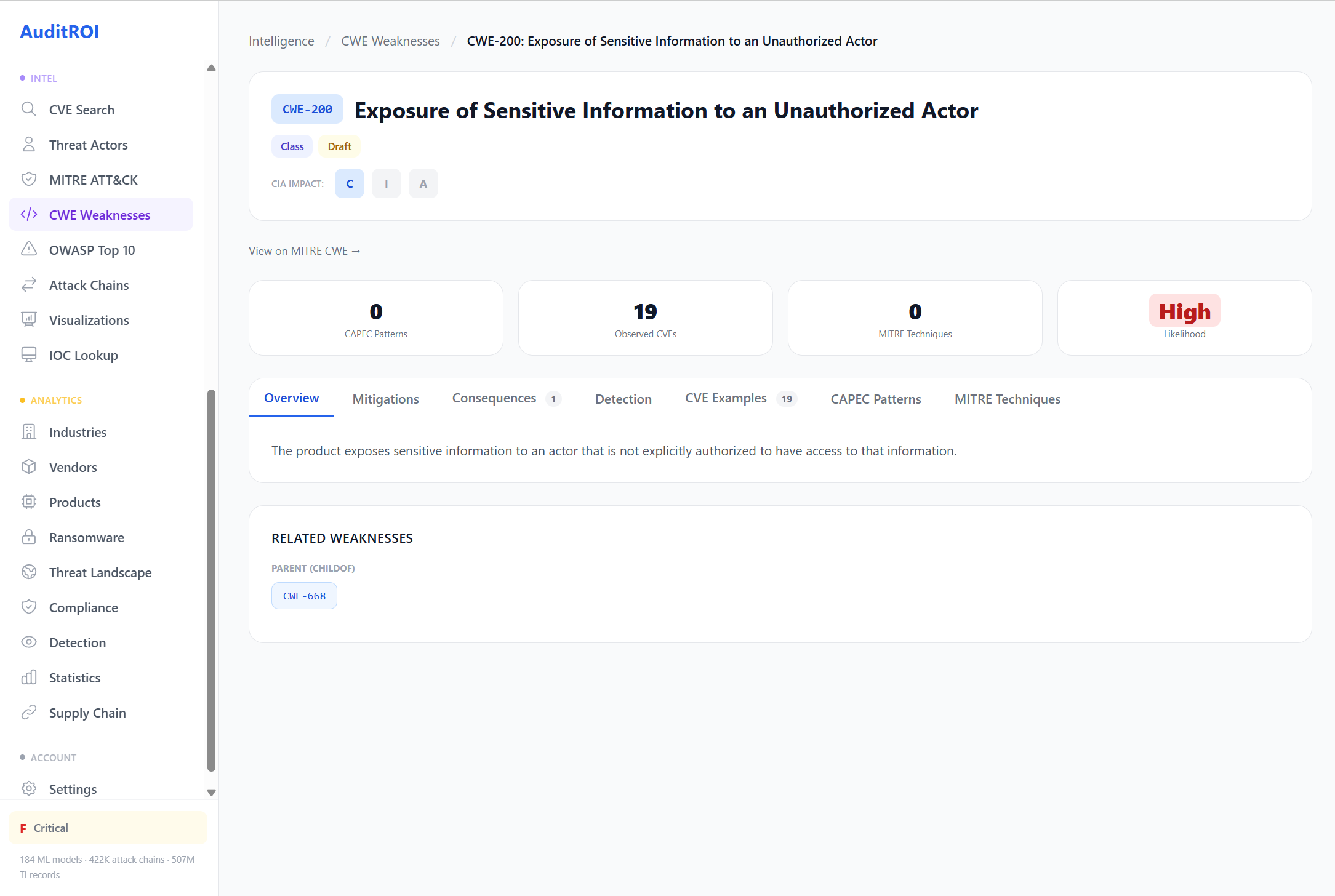
CWE Weakness Database
Common Weakness Enumeration catalog with CAPEC attack patterns, mitigations, and severity ratings.
Each weakness links to related CVE examples, MITRE techniques, and detection rules. Filter by category: Web, Injection, Auth, Crypto, Memory.
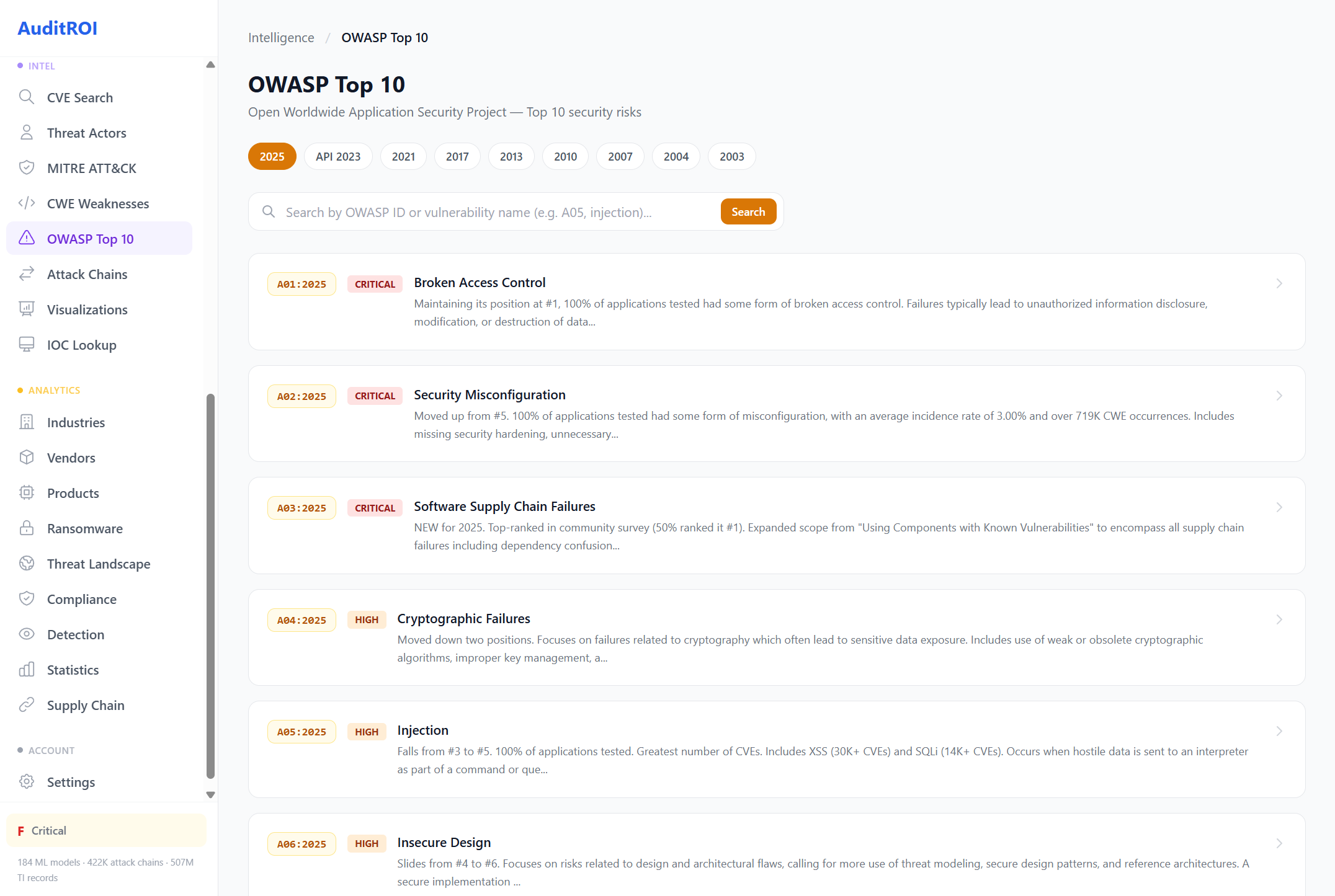
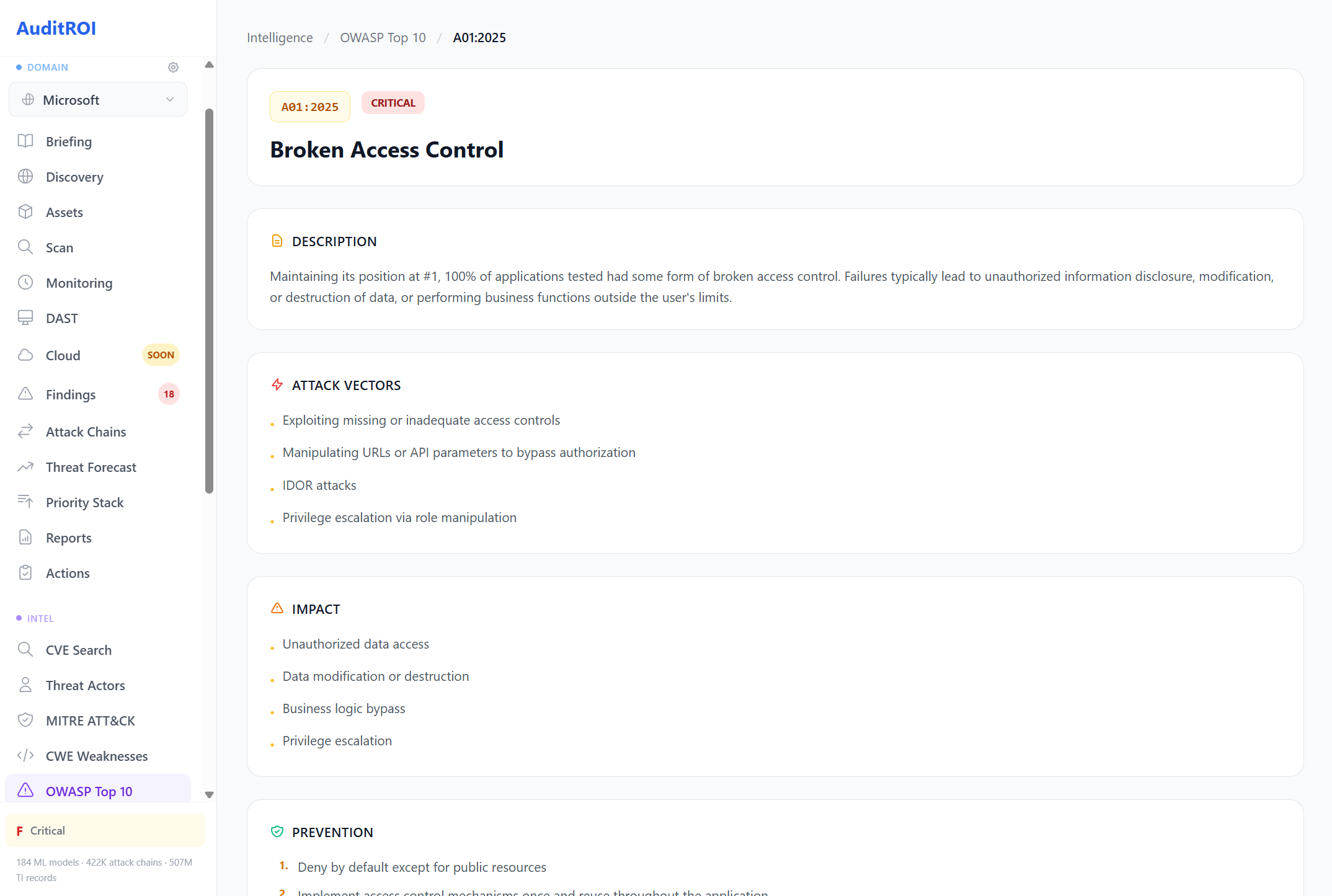
OWASP Top 10
Every OWASP version (2025, 2021, 2017 and earlier) with attack vectors, impact analysis, and prevention guidance.
Each entry includes descriptions, real-world examples, and specific controls. Mapped to your scan findings so you know exactly where you stand.
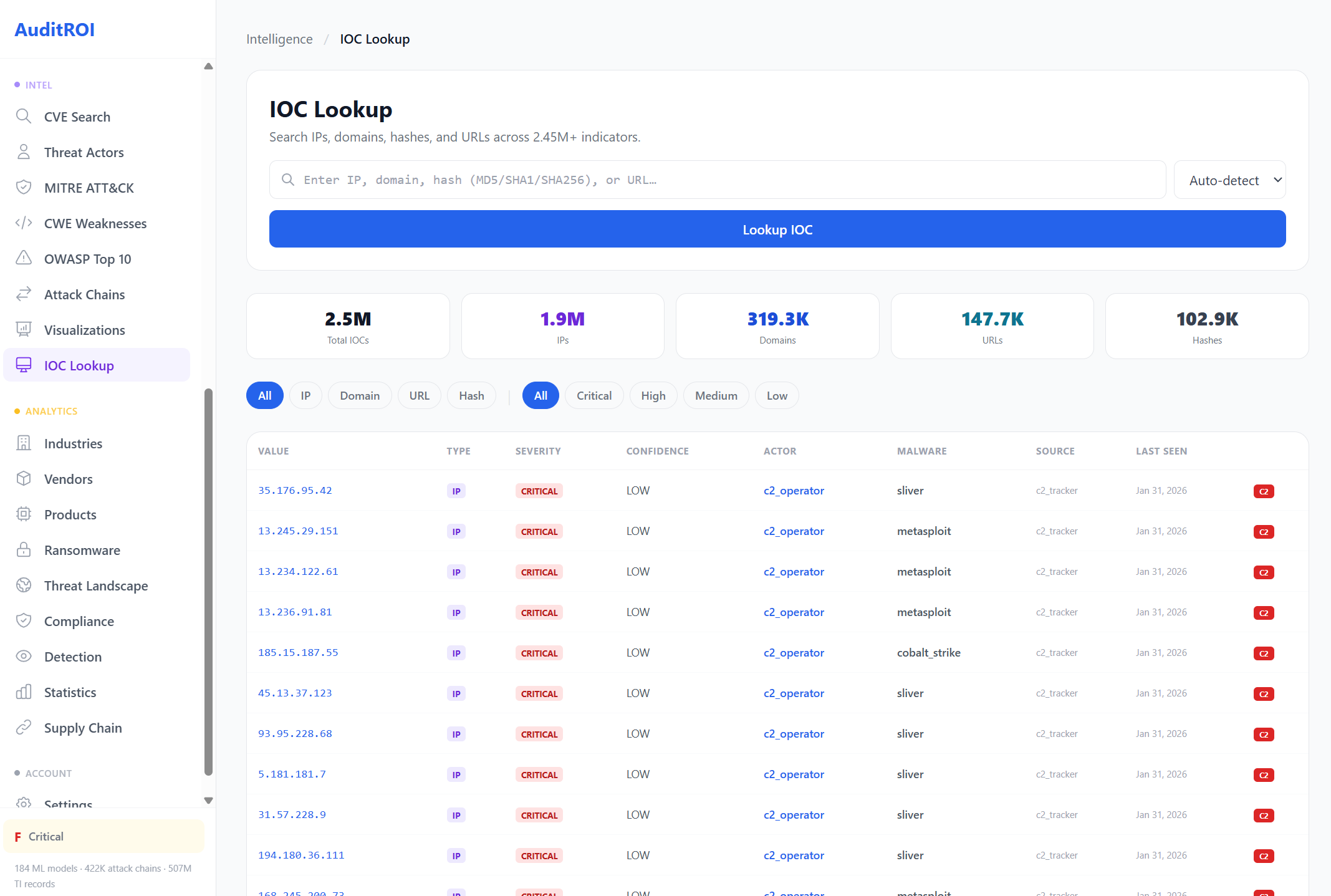
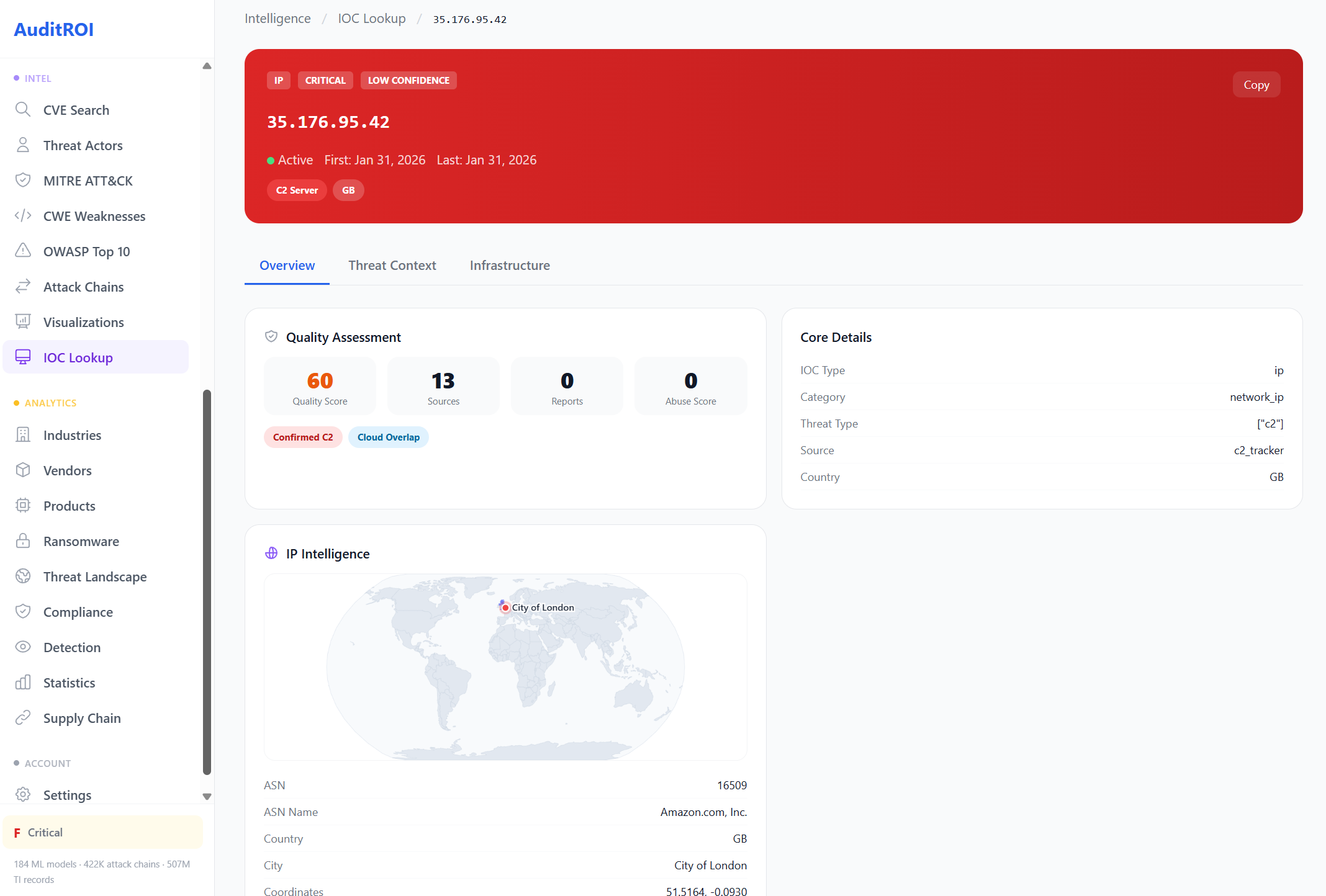
IOC Lookup
Search IPs, domains, hashes, and URLs across 2.43M+ indicators of compromise with threat context.
Each result includes a quality score, geolocation map, ASN data, threat actor attribution, and infrastructure details. Auto-detects indicator type.
Detection Engineering
21,000+ detection rules mapped to 1,042 MITRE ATT&CK techniques.
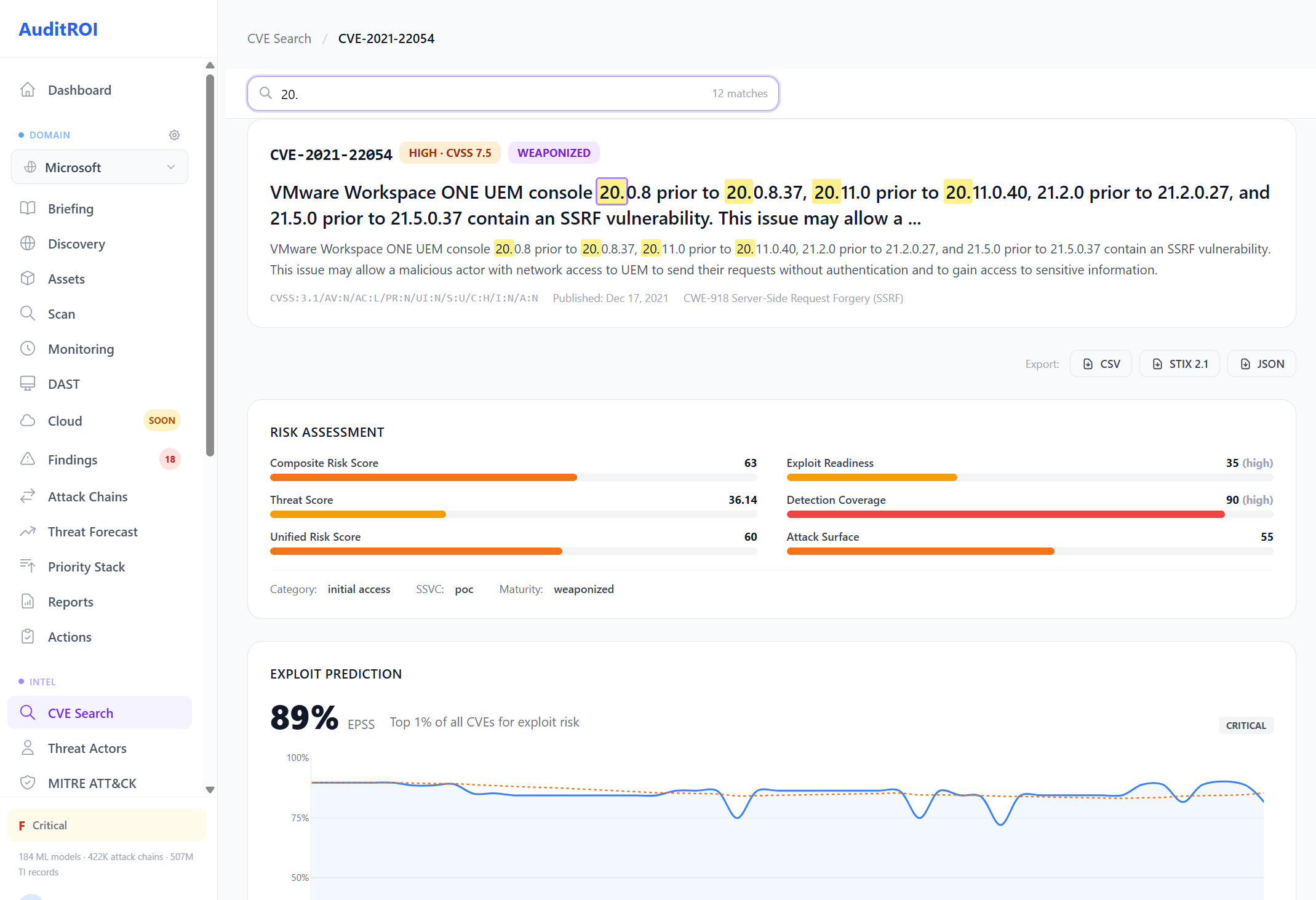
Get Threat-Enriched Results
Every vulnerability cross-referenced against 507M+ threat intelligence records.